I sincerely hope you didn’t get infected by WannaCry, but I’m pretty sure most of you where working extra hours to make sure to get all your systems up to date.
Now, you might have been lucky this time, but the next time you might not be unless you change your patching strategy. Windows Patching As We Know It Is Dead!

First of all make sure you have a Windows Server Updates Services with an Automatic Approvals Rule. If not you can follow the post Automate WSUS on Windows 2016 Server Core.
Let’s make Microsoft handle Security Updates. Better Safe than Sorry!
Make sure you have a Group Policy that applies to all your Computers that specify WSUS location, installation schedule etc.

Monitor the WSUS console on a daily basis to make sure that all your Computers is 100% updated, if not investigate and resolve the issues.
The new way of patching going forward is to automatically build your Master Images from scratch EACH AND EVERY WEEK on a schedule. In fact, rumors says Citrix Systems is doing the exact same thing.

The old school way would be to open the Master Image, doing the updates, adding new applications and then doing the sealing process. The biggest problem with this approach is that is doesn’t happen on a regular basis. I’ve seen 80.000 seat customers doing updates every second month or even worse twice a year!
Why is that? Probably because there’s to many Master Images and there’s no Automated solutions to handle this, everything is manual work. There’s a lot of stuff that can go wrong…
As I did predict last year, ransomware is going to be HUGH this year, and we’ve just seen the tip of the iceberg.

I’ve confirmed stories from 8 companies getting hit by ransomeware and paying out $100.000 each only last year in the UK. These stories never hits the press. Security is more important than ever, and this was also the clear message here at Citrix Synergy 2017.
The New School Way
So what is the recommended way going forward? Automation of course.
Windows Updates and more importantly virus patterns gets updated at least once a week. Running MCS or PVS Non-Persistent Desktops simply cannot handle this in a good fashion, even worse if you’re using the manual method.

The Automation Tools in use is not important, what’s important is that you have a scheduled 100% automated solution to automatically rebuild your Master Image(s) on a weekly basis.
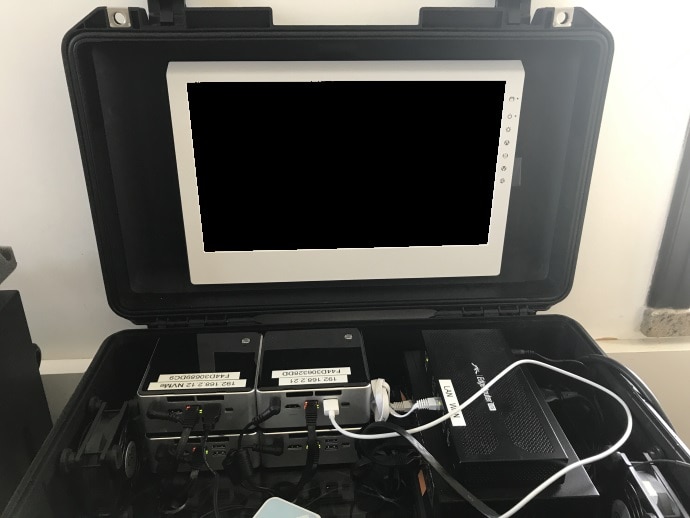
It’s not a coincidence that my 3 Day Automation Framework Master Class has become extremely popular and I’m flying around the world teaching my classes each and every month. In fact I just build a new Data Center in a Box that will be used in Europe and lead by my fellow CTP Dave Brett.

I have explored this method of updating XenApp 6.5 servers used as Hosted App servers and it works very well. However, I ran into issues with Hosted Desktop hosts because of the need to customize the default profile configurations (Non-Appsense). I know MDT does support the creation of default profile but it is rather tricky and I haven’t found any easy to follow methods of using it for building custom Citrix XenApp published desktop hosts.