When you configure NetScaler Gateway for testing you probably do like me and configure HTTP (80) for everything instead of HTTPS (443) which is a little bit more work.
The main reason why you would and should switch to HTTPS is not because of security, but User Experience. You see, for users to be able to change expired passwords through NetScaler you need to use Secure LDAP (636). Let’s get started!
The first thing you need to do is to setup Active Directory Certificate Services, Create a Domain Certificate and export it. The blog post Securing Citrix X1 StoreFront with Powershell will show you how.
Open Citrix Studio – StoreFront – Server Group – Change Base URL and change from HTTP to HTTPS.

Citrix Studio – StoreFront – Stores – Manage Delivery Controllers – Edit.

Connect to StoreFront through SSL and verify that your certificate is valid.

After testing that SSL works okay it’s time to configure NetScaler.
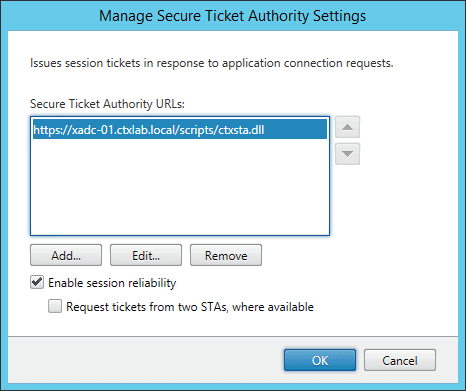
Citrix Studio – NetScaler Gateway – Secure Ticket Authority – Edit.
Check the post Convert .PFX Certificate to PEM Format from Carl Stalhood on how to import and install your Domain Certificate on NetScaler.
Navigate to the NetScaler LDAP policy – edit Server and select SSL from the drop-down list.

A tip from David shows that you can also use SSL.

Change STA from HTTP to HTTPS.

Edit the PL_OS Profile.

Edit the PL_WB Profile.


Save the settings and reboot the NetScaler Gateway.
Set your test users password to expired and log in.


And that’s it.
Pretty sure from 2012 R2 LDAPS also works with the standard LDAP port too.
Whoops, shouldn’t have skipped through the article.
While the NetScaler supports multiple options, using StartTLS, which is the tip David Pisa posted, is the easier way to secure the traffic. Basically, the LDAP communication starts as plain text over port 389, but a TLS session is negotiated before the data is sent. The advantage is that it is simpler to setup (same port) and most modern OS support it. See RFC2830 for specifics on StartTLS and LDAP.
http://docs.citrix.com/en-us/netscaler-gateway/11/authentication-authorization/configure-ldap.html
I agree with the need to go secure, but disagree with your reasoning. Most users don’t have a clue about the differences between http and https, or even care. They generally assume http when they type in a URL, because the browser lets them. This is why I appreciate the NetScaler having responder policies… 😉
Hi Mark, thanks for your comments. For UX I was referring to users beeing able to change password instead of denied login.