Last year when working on my Automation Framework 1909 release I spun up a new lab and enabled port forwarding to be able to access that particular vLAN from home. I’m well aware of the risk of RDP hacking and that’s why I enabled the forwarding rule when I started to work that Saturday morning.

The reason I got hacked is obvious, weak P@ssw0rd and default port 3389. Now the scary part is how fast it happened. Less than 3 hours later I was hacked!
Today to prevent RDP hacking I never enable RDP access without a 2-Factor Authentication (2FA) solution. You’ll be surprised at how fast and easy it is to setup using Parallels Remote Application Server.
You will need two servers, one being the Gateway and the other being the jump host / worker. You can deploy it all automatically (including software download) using my video instructions from my free Automation Framework Community Edition.
I’m running the infrastructure on Windows 2019 Server Core using 1 vCPU with 2 GB. The only thing you need to do is to register for a Parallels account and replace the info below before running the PowerShell code below.
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 |
Import-Module PSAdmin Set-NetFirewallProfile -Profile Domain -Enabled False $Server = "YOURINFRASERVER" $User = "administrator@YOURDOMAIN" $Pwd = "YOURPASSWORD" $Password = ConvertTo-SecureString $Pwd -AsPlainText -Force $Email = "PARALLELS ACCOUNT EMAIL" $EmailPwd = "PARALLELS ACCOUNT PASSWORD" $EmailPassword = ConvertTo-SecureString $EmailPwd -AsPlainText -Force New-RASSession -Username $User -Password $Password -Server $Server $RDS1 = New-RDS -Server "YOURWORKERSERVER" $RDSList = Get-RDS New-RDSGroup -Name "Windows 2019 RDS" -RDSObject $RDSList Set-RDSDefaultSettings -MaxSessions 100 -EnableAppMonitoring $true New-PubRDSDesktop -Name "Desktop" Set-RASTurboSettings -Enable $False Set-2FASetting -Provider GAuthTOTP Invoke-LicenseActivate -email $Email -Password $EmailPassword Invoke-Apply |
My worker is running Windows 2019 Server with Desktop Experience using 2 vCPU with 4 GB. Run the following configuration in PowerShell on the Worker.
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 |
Import-Module PSAdmin $Server = "YOURINFRASERVER" $User = "administrator@YOURDOMAIN" $Pwd = "YOURPASSWORD" $Password = ConvertTo-SecureString $Pwd -AsPlainText -Force New-RASSession -Username $User -Password $Password -Server $Server New-PubRDSApp -Name "Word 2016" -Target "C:\Program Files (x86)\Microsoft Office\root\Office16\WINWORD.EXE" -Icon "C:\Program Files (x86)\Microsoft Office\root\Office16\WINWORD.EXE" -IconIndex 0 New-PubRDSApp -Name "Excel 2016" -Target "C:\Program Files (x86)\Microsoft Office\root\Office16\EXCEL.EXE" -Icon "C:\Program Files (x86)\Microsoft Office\root\Office16\EXCEL.EXE" -IconIndex 0 New-PubRDSApp -Name "PowerPoint 2016" -Target "C:\Program Files (x86)\Microsoft Office\root\Office16\POWERPNT.EXE" -Icon "C:\Program Files (x86)\Microsoft Office\root\Office16\POWERPNT.EXE" -IconIndex 0 New-PubRDSApp -Name "Outlook 2016" -Target "C:\Program Files (x86)\Microsoft Office\root\Office16\OUTLOOK.EXE" -Icon "C:\Program Files (x86)\Microsoft Office\root\Office16\OUTLOOK.EXE" -IconIndex 0 New-PubRDSApp -Name "Google Chrome" -Target "C:\Program Files (x86)\Google\Chrome\Application\chrome.exe" -Icon "C:\Program Files (x86)\Google\Chrome\Application\chrome.exe" -IconIndex 0 New-PubRDSApp -Name "FireFox" -Target "C:\Program Files\Mozilla Firefox\firefox.exe" -Icon "C:\Program Files\Mozilla Firefox\firefox.exe" -IconIndex 0 New-PubRDSApp -Name "Acrobat Reader DC" -Target "C:\Program Files (x86)\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" -Icon "C:\Program Files (x86)\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" -IconIndex 0 Invoke-Apply |
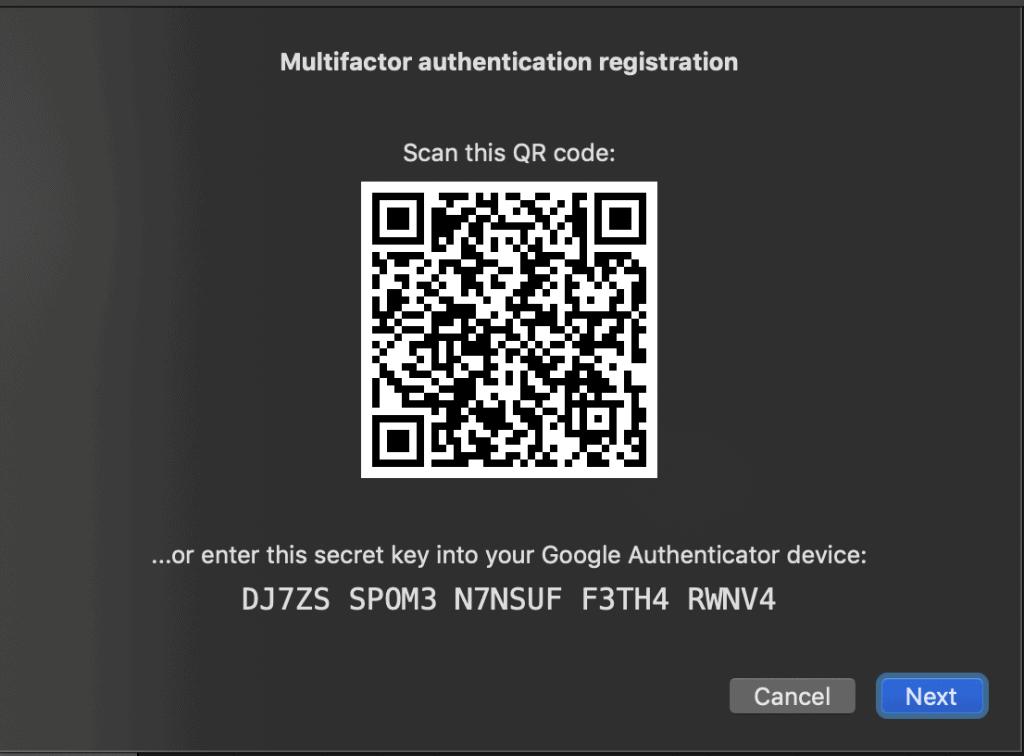
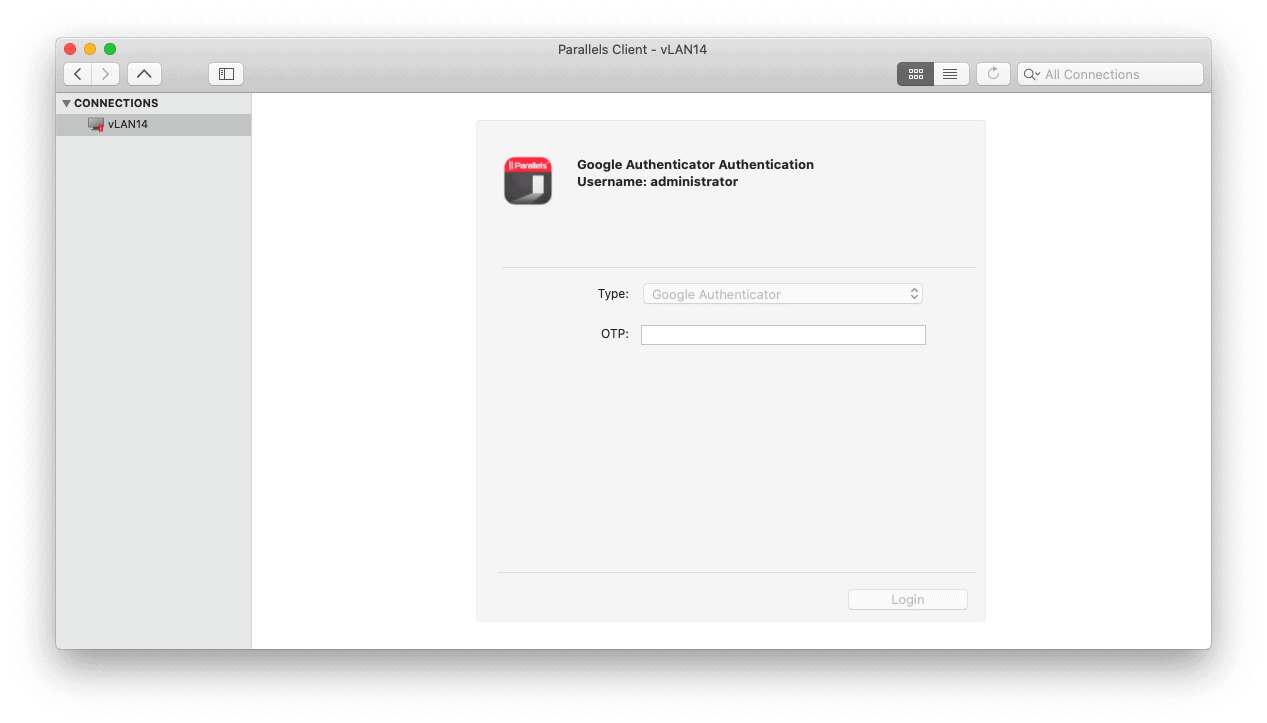
To active 2-Factor Authentication, open http://INFRASERVERSERVER and logon with the AD account you want to use for remote access. This will display a QR code that you need to scan into your Google or Microsoft Authenticator app.

And that’s a simple way to prevent RDP hacking. Parallels is extremely easy and fast to implement and did I mention the price? It’s only $99 per user/year.
Have you tried Guacamole?
It’s pretty easy to setup and has OTP right out the box.
https://guacamole.apache.org/
I’m using it to access my lab
Thanks Val